access control list (ACL)
What is an access control list (ACL)?
An access control list (ACL) is a list of rules that specifies which users or systems are granted or denied access to a particular object or system resource. Access control lists are also installed in routers or switches, where they act as filters, managing which traffic can access the network.
Each system resource has a security attribute that identifies its access control list. The list includes an entry for every user who can access the system. The most common privileges for a file system ACL include the ability to read a file or all the files in a directory, to write to the file or files, and to execute the file if it is an executable file or program. ACLs are also built into network interfaces and operating systems (OSes), including Linux and Windows. On a computer network, access control lists are used to prohibit or allow certain types of traffic to the network. They commonly filter traffic based on its source and destination.
What are access control lists used for?
Access control lists are used for controlling permissions to a computer system or computer network. They are used to filter traffic in and out of a specific device. Those devices can be network devices that act as network gateways or endpoint devices that users access directly.
On a computer system, certain users have different levels of privilege, depending on their role. For example, a user logged in as network administrator may have read, write and edit permissions for a sensitive file or other resource. By contrast, a user logged in as a guest may only have read permissions.
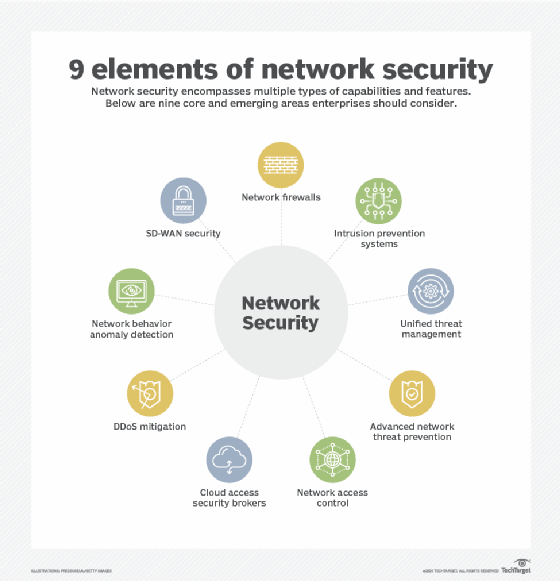
Access control lists can help organize traffic to improve network efficiency and to give network administrators granular control over users on their computer systems and networks. ACLs can also be used to improve network security by keeping out malicious traffic.
How do ACLs work?
Each ACL has one or more access control entries (ACEs) consisting of the name of a user or group of users. The user can also be a role name, such as programmer or tester. For each of these users, groups or roles, the access privileges are stated in a string of bits called an access mask. Generally, the system administrator or the object owner creates the access control list for an object.
Types of access control lists
There are two basic types of ACLs:
- File system ACLs manage access to files and directories. They give OSes the instructions that establish user access permissions for the system and their privileges once the system has been accessed.
- Networking ACLs manage network access by providing instructions to network switches and routers that specify the types of traffic that are allowed to interface with the network. These ACLs also specify user permissions once inside the network. The network administrator predefines the networking ACL rules. In this way, they function similar to a firewall.
ACLs can also be categorized by the way they identify traffic:
- Standard ACLs block or allow an entire protocol suite using source IP addresses.
- Extended ACLs block or allow network traffic based on a more differentiated set of characteristics that includes source and destination IP addresses and port numbers, as opposed to just source address.
Benefits of using an ACL
There are several benefits of using an ACL, including the following:
- Simplified user identification. An access control list simplifies the way that users are identified. ACLs ensure that only approved users and traffic have access to a system.
- Performance. ACLs provide performance advantages over other technologies that perform the same function. They are configured directly on the routing device's forwarding hardware, so access control lists do not have a negative performance effect on routing devices. Compare this to a stateful inspection firewall, which is a separate piece of software that may cause performance degradation. Also, controlling network traffic enables networks to be more efficient.
- Control. ACLs can give administrators more granular control over user and traffic permissions on a network at many different points in the network. They help control access to network endpoints and traffic flowing between internal networks.
Where can you place an access control list?
Access control lists can be placed on virtually any security or routing device, and having multiple ACLs in different parts of the network can be beneficial.
ACLs are well suited to network endpoints -- like applications or servers -- that require high speed and performance, as well as security.
Network administrators may choose to place an access control list at different points in the network depending on the network architecture. ACLs are often placed on the edge routers of a network because they border the public internet. This gives the ACL a chance to filter traffic before it reaches the rest of the network.
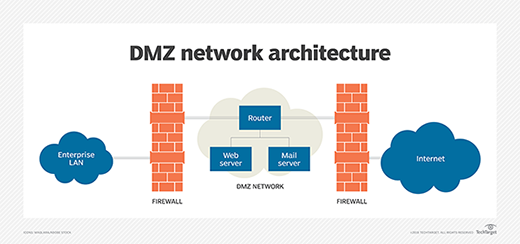
Edge routers with ACLs can be placed in the demilitarized zone (DMZ) between the public internet and the rest of the network. A DMZ is a buffer zone with an outward-facing router that provides general security from all external networks. It also features an internal router that separates the DMZ from the protected network.
DMZs may contain different network resources, like application servers, web servers, domain name servers or virtual private networks. The configuration of the ACL on the routing device is different, depending on the devices behind it and the categories of user that need access to those devices.
Components of an access control list
ACL entries consist of several different components that specify how the ACL treats different traffic types. Some examples of common ACL components include the following:
- Sequence number. The sequence number shows the identity of the object in the ACL entry.
- ACL name. This identifies an ACL using a name instead of a number. Some ACLs allow both numbers and letters.
- Comments. Some ACLs enable users to add comments, which are extra descriptions of the ACL entry.
- Network protocol. This enables admins to allow or deny traffic based on a network protocol, such as IP, Internet Control Message Protocol, TCP, User Datagram Protocol or NetBIOS, for example.
- Source and destination. This defines a specific IP address to block or allow or an address range based on Classless Inter-Domain Routing.
- Log. Some ACL devices keep a log of objects that the ACL recognizes.
More advanced ACL entries can specify traffic based on certain IP packet header fields, like Differentiated Services Code Point, Type of Service or IP precedence.
How to implement an ACL
To implement an ACL, network administrators must understand the types of traffic that flow in and out of the network, as well as the types of resources they are trying to protect. Administrators should hierarchically organize and manage IT assets in separate categories and administer different privileges to users.
A standard ACL list is generally implemented close to the destination that it is trying to protect. Extended access control lists are generally implemented close to the source. Extended ACLs can be configured using access list names instead of access list numbers.
The basic syntax used to create a standard numbered access control list on a Cisco router is as follows:
Router (config)# access-list (1300-1999) (permit | deny) source-addr (source-wildcard)
The various parts mean the following:
- (1300-1999) specifies the ACL IP number range. This names the ACL and defines the type of ACL. 1300-1999 makes this a standard ACL.
- (permit | deny) specifies the packet to permit or reject.
- Source-addr specifies the source IP address.
- Source-wildcard specifies the wildcard mask.
A wildcard mask tells a router which bits of an IP address are available for a network device to examine and determine if it matches the access list.
Users can enter the above configuration code into the command line to create the access control list. Cloud platforms from vendors, including Oracle and IBM, also typically offer an option to create an access control list in their user login portal.
Setting user permissions throughout a computer system can be tedious, but there are ways to automate the script.
Access control lists must be configured differently based on differences in network architecture. This includes differences between on-premises, physical networks and cloud networks. Learn the basics of cloud network architecture and network management.








