
business continuity
What is business continuity?
Business continuity is an organization's ability to maintain critical business functions during and after a disaster has occurred. Business continuity planning establishes risk management processes and procedures that aim to prevent interruptions to mission-critical services and reestablish full day-to-day function to the organization as quickly and smoothly as possible.
The most basic business continuity requirement is to keep essential functions up and running during a disaster and to recover with as little downtime as possible. A business continuity plan is a framework that considers unpredictable events and potential threats, such as natural disasters, fires, disease outbreaks, pandemics, supply chain disruptions, cyber attacks and other external threats.
Although a business continuity strategy is important for organizations of all sizes, it might not be practical for any but the largest enterprises to maintain all functions for the duration of a disaster. According to many experts, the first step in business continuity and disaster recovery planning is deciding what functions are essential and allocating the available budget accordingly. Once crucial components have been identified, administrators can put failover mechanisms in place.
Technologies such as disk mirroring enable an organization to maintain up-to-date copies of data in geographically dispersed locations, not just in the primary data center. This helps data access functions continue uninterrupted if one location is disabled and protects against data loss.
Why is business continuity important?
Downtime is costly and disruptive, making business continuity critical. Threats that can cause downtime, such as cyberattacks and extreme weather, seem to be getting worse. According to Gartner, cyber attacks are becoming more sophisticated and exploiting poor cybersecurity threat detection. Therefore, it's important to have a business continuity plan in place that can help an organization maintain its critical functions after an emergency or disruption.
The plan should enable the organization to keep running at least at a minimal level during a crisis. Business continuity helps the organization maintain resiliency in responding quickly to an interruption. Strong business continuity saves money, time and company reputation. An extended outage risks financial, personal and reputational loss.
Business continuity requires an organization to look at itself, analyze potential areas of weakness and gather key information -- such as contact lists and technical diagrams of systems -- that can be useful outside of disaster situations. In undertaking the business continuity planning process, an organization can improve its communication, technology and resilience.
Business continuity might even be a requirement for legal or compliance reasons. It's important to understand which regulations affect a given organization, especially in an era of increased regulation.
What does business continuity include?
Business continuity is a proactive way to ensure mission-critical business operations continue during a disruption or in the event of a disaster. A successful business continuity plan includes the following:
- Clear and comprehensive guidelines. Business continuity features clear guidelines for what an organization must do to maintain operations. If the time comes for action, there should be no question about how to move forward with business processes. The plan should have contact information, steps for what to do when faced with a variety of incidents and a guide for when to use the document.
- Defined levels of response. Proper business continuity includes different levels of response. Not everything is mission-critical, so it's important to lay out what is most vital to keep running and what could come back online at later times. It's crucial to be honest about recovery time objectives (RTOs) and recovery point objectives (RPOs).
- A flexible response. A business continuity plan should be created to deal with any potential risks. An organization should determine how these risks will affect operations and should use the business continuity plan to outline the implementation of safeguards and procedures in case of a disaster. Testing procedures should also be put in place, along with a detailed process to ensure the plan is kept current.
- A collaborative and transparent process. The business continuity process includes the whole organization -- from executive management on down. Although IT might drive the process, it's essential to get buy-in from management and other stakeholders and to communicate key information to the entire organization. Everyone should know the basic steps for how the organization plans to respond. An important area of collaboration is with the security team; although IT and the security team often work separately, an organization benefits when the two departments share information.
3 key components of a business continuity plan
A business continuity plan has three key elements: resilience, recovery and contingency.
Resilience. An organization can increase its resilience by designing critical functions and infrastructure with various disaster possibilities in mind; this can include staffing rotations, data redundancy and maintaining a surplus of capacity. Ensuring business resiliency against different scenarios can also help organizations maintain essential services on- and off-site without interruption.
Recovery. Rapid recovery to restore business functions after a disaster is crucial. Setting RTOs for different systems, networks or applications can help prioritize which elements must be recovered first. Other recovery strategies include resource inventories, agreements with third parties to take on company activity and using converted spaces for mission-critical functions.
Contingency. A contingency plan has procedures in place for a variety of external scenarios and can include a chain of command that distributes responsibilities within the organization. These responsibilities can include hardware replacement, leasing emergency office spaces, damage assessment and contracting with third-party vendors for assistance.
Business continuity standards
Table 1 lists the standards in the International Standards Organization (ISO) 223XX series that apply to business continuity and related activities. The Business Continuity Institute (BCI) also provides global business continuity standards and best practices in its Good Practices Guidelines. Those standards and guidelines -- along with several from the U.K., including the British Standards Institute's "Guidance on organization recovery following disruptive incidents" and "Organizational Resilience Framework" -- map closely to the ISO 22301 standard.
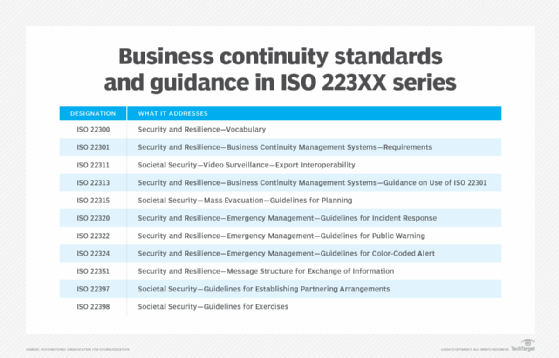
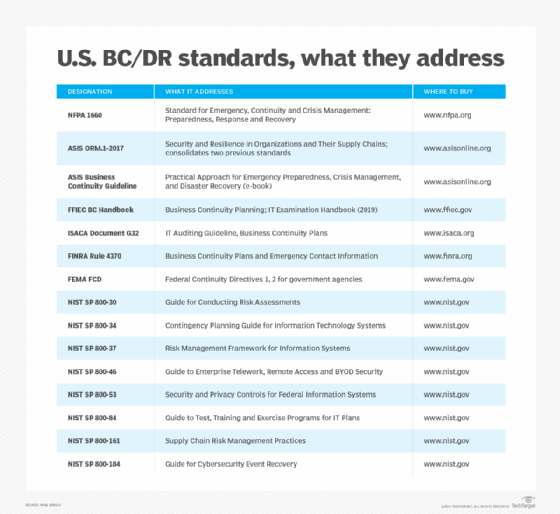
Table 2 provides a partial listing of standards, regulations and good practices developed in the U.S. by several different organizations, including ASIS International, the Federal Emergency Management Agency (FEMA), the Federal Financial Institutions Examination Council (FFIEC), the Financial Industry Regulatory Authority (FINRA), Information Systems Audit and Control Association (ISACA), the National Fire Protection Association (NFPA) and the National Institute for Standards and Technology (NIST).
Business continuity plans should be adaptable
One method of instituting a business continuity plan is to perform a risk assessment of an organization's processes and then build a response plan for each instance of a risk. This can help the organization identify potential risks to the business and prepare for unexpected challenges, ensuring it's adaptable in the event of a disaster.
An organization that builds a more elastic and adaptable business continuity plan will be able to minimize the effects of numerous types of attacks and vulnerabilities. A business continuity plan should focus on resilience and flexibility and detail how to respond to potential cyber and ransomware threats across an organization's access points.
As opposed to assessing and reacting to potential disruptions, a flexible business continuity plan aligns an organization's technology, operations, processes and people -- ensuring the organization can quickly adjust and adapt to an emerging issue while mitigating its potential impacts.
Business continuity vs. disaster recovery
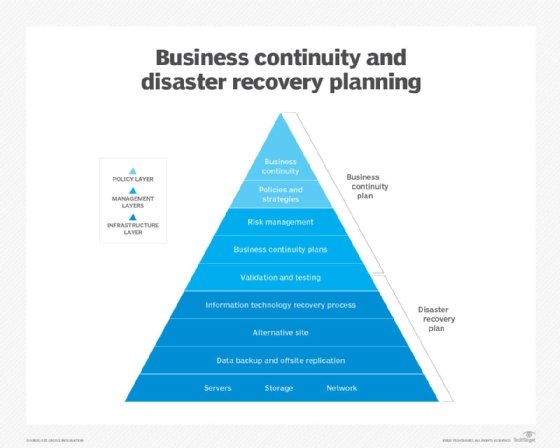
Like a business continuity plan, disaster recovery planning specifies an organization's planned strategies for post-failure procedures. However, a disaster recovery plan is just a subset of business continuity planning.
One of the main differences between the two is that, while business continuity focuses on keeping businesses operational throughout a disaster, a disaster recovery plan places its focus on the process of restoring data and infrastructure access after a disaster.
Disaster recovery plans are mainly data-focused and concentrate on having adequate data backup and storing data in a way that makes it easily accessible following a disaster. Business continuity takes this into account but also focuses on risk management, oversight and planning for an organization that needs to stay operational during a disruption. Business continuity also focuses on providing employee safety measures.
Business continuity development
Business continuity planning starts with initiating the planning project. Business impact analysis (BIA) and risk assessment are essential steps in gathering information for the plan. They offer the following benefits:
- Business impact analysis. Conducting a BIA can reveal possible weaknesses as well as the consequences of a disaster on various departments. The BIA report informs an organization of the most crucial functions and systems to prioritize in a business continuity plan.
- Risk assessment. A risk assessment identifies potential hazards to an organization, such as natural disasters, power outages, cyber attacks and technology failures. Risks can affect staff, customers, building operations and company reputation. The assessment also details what or whom a risk could harm and the risk likelihood.
The BIA and risk assessment work jointly. The BIA provides details as to the potential effects of the possible disruptions outlined in the risk assessment.
An organization should also have a defined RTO and RPO. An RTO defines the target amount of time between a failure and the resumption of operations. The RPO, by comparison, is the amount of data loss that an organization can endure. The RTO and RPO values can change from organization to organization based on several factors, including business and regulatory requirements.
Business continuity management
It's important to designate who will manage the business continuity program should a business disruption occur. It could be one person if it's a small business or a whole team for a larger organization. Business continuity management software is also an option. Software -- either on premises or cloud-based -- helps conduct BIAs, create and update plans and pinpoint areas of risk.
Business continuity is an evolving process. As such, an organization's business continuity plan shouldn't just sit on a shelf. The organization should communicate its contents to as many people as possible. Implementation of business continuity isn't just for times of crisis; the organization should have regular training exercises, so employees know what they'll be doing in the event of an actual disruption.
Business continuity testing is critical to its success. It's difficult to know if a plan is going to work if it hasn't been tested. A business continuity test can be as simple as a tabletop exercise where staff discuss what will happen in an emergency. More rigorous testing includes a full emergency simulation. An organization can plan the test in advance or perform it without notice to better mimic a crisis.
Once the organization completes a test, it should review how it went and update the crisis management plan accordingly. It's likely that some parts of the plan will go well, but other actions might need adjusting. A regular schedule for testing is helpful, especially if the business changes its operations and staff frequently. Comprehensive business continuity undergoes continual testing, review and updating.
What tools can be used in business continuity?
Organizations use a variety of methods and tools to implement business continuity plans, including the following:
- Backup. This is the process of copying physical or virtual files or databases to a secondary location for preservation in case of equipment failure or a malicious attack. This is one of the simpler processes for implementing business continuity.
- Backup as a service. A third-party provider backs up data at a secondary location using a private, public or hybrid cloud service.
- Disaster recovery as a service. In the event of a disaster, an organization moves its computer processing to the third-party DRaaS provider's cloud infrastructure. The DRaaS provider serves as the disaster recovery site when a disaster is declared.
- Virtualization. Virtualization uses software that simulates hardware functionality, creating a virtual system. The virtual system can back up a working replica of an organization's computing environment.
- Point-in-time recovery. These are snapshots of an organization's database, which are taken at regular intervals. For business continuity purposes, these snapshots can be stored in a secondary location and can be used to restore data.
- Cold site. A cold site is a basic infrastructure set up in a secondary location. Cold sites are essentially available space with minimal infrastructure set up in it. This stays true until a disaster occurs and the organization sets up more infrastructure and resources.
- Hot site. A hot site is a copy of a data center with all the organization's hardware and software running concurrently with its primary site. A hot site provides redundancy, essentially acting as a second data center. When experiencing a disaster, an organization with a hot site will experience minimal to no downtime.
Business Continuity Institute
The BCI is a global professional organization that provides education, research, professional accreditation, certification, networking opportunities, leadership and guidance on business continuity and organizational resilience.
The U.K.-based organization was established in 1994 and includes 9,000 members in more than 120 countries, in the public and private sectors. Business continuity professionals and those interested in the field can use the products and services available from the BCI.
The BCI's objectives and work include raising standards in business continuity, sharing business continuity best practices, training and certifying business continuity professionals, raising the value of the profession and developing the business case for business continuity.
The institute's many published resources include its Good Practice Guidelines document, which offers guidance for identifying business continuity activities that can support strategic planning.
Professional membership in the BCI conveys an internationally recognized status, while certification demonstrates a member's proficiency in business continuity management.
Chapters of the BCI have been established in countries or regions where there's a large community of members. The chapters, which include the U.S., Japan and India, have locally elected officers who represent the BCI in their region.
Business continuity plans vary from organization to organization, depending on the specific risks they face. Learn the top business continuity risks to monitor.








